I´m curious about how Plex would handle such a scenario, where the server has multiple local IPs on different subnets and one external IP.
For example:
1: 192.168.1.10
2: 10.10.2.12
3: some external IP
Is plex.direct grabbing all IPs the server has and sends them to the player, so the player can try to reach one of them? Like Player A is in Subnet 2 and gets 1: 192.168.1.10, 2: 10.10.2.12, and the external IP, it can not reach Subnet 1 but Subnet 2 and therefore should use and connect to 10.10.2.12, would that work?
PMS will always listen on and base Remote Access (external IP) on the default adapter of the host. (This is usually the first adapter defined)
When “Preferred Adapter” is set to any (default), it will accept traffic on the other adapters.
Thanks! And when “Preferred Adapter” is set to any (default), plex.direct also grabs all the other host/server ips? Or I should ask differently how many ips does plex store for one server?
Question: Why would you want to put multiple IPs on your server?
Why would you?
Normal HOME configurations only have one address.
There is no normal configuration where a HOME LAN should need multiple subnets (no added security by doing so) but there are those who feel VLANing their traffic is of benefit.
My personal feelings on the subject are
-
If an intruder is on your LAN, regardless of which subnet, there is a much bigger problem to be resolved – How did the intrusion occur
-
There can be benefit to VLANing specific devices into classes (e.g. IOT devices, childrens’ tablets / phones) where you want physical isolation from core services at the switching layer.
For me, I have the guest VLAN and main VLAN present on the AP.
Devices are classified by MAC address.
Those allowed on the MAIN VLAN are given a core subnet address
Guests, who get DHCP addresses, go to the guest VLAN by default.
Guest devices have no access to my PMS server
I still maintain, even in this configuration , one PMS server address
PMS reports all the adapter IPs that it sees on its host.
If you have multiple subnets, you’ll drive your modem/router crazy because you’ll be performing multiple DNS rebinding actions (one per subnet). Most will tolerate one but rarely more than that would manual configuration in the DNS resolver.
Not only that, if you are on the same physical segment, your router becomes a one-armed router between subnets, further spending CPU cycles and memory on that.
The need to segment is warranted, but I use VLANs. I also do my filtering between my Guest, IoT devices and the rest of my network at my router. IoT are not allowed to talk to anything except my PiHole servers (DNS) on my internal network, otherwise they can only talk to the Internet and each other.
Guests are only allowed to my Plex server and PiHole servers and the Internet. They are NOT allowed to talk to each other.
My internal network is allowed to talk to anyone inside the network, but not the IoT or Guests.
I thought about moving my TVs and server to a streaming VLAN but, my smart remotes need Layer-2 to them, as well as if I ever want to control my TVs and streaming devices from my phone. I kind of wish there was a way to statically IP devices and set the IP so I can do that but in the consumer electronics industry’s incredible knowledge of security, they neglect that in order to give convenience.
Thanks for all the answers!
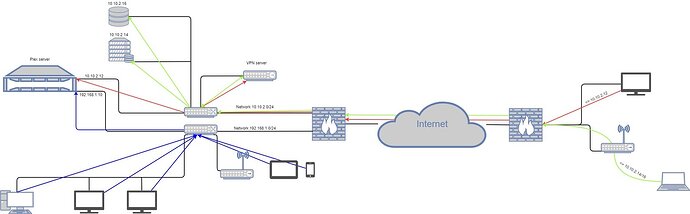
The idea behind my question is this scenario.
I hope it is not too confusing. The idea is to have a secondary site with access to only the 10.10.2.0/24 subnet and the services exposed there including plex, but I don’t want my local devices to have access to these services but only to the plex server => so they are in their own network (192.168.1.0/24)… There comes my question on how do they know which ip they should use for the plex server because so the server has two ips. I don’t want to do (Inter-) VLAN routing, as the router is already doing stuff like Suricata… Do you think DNS rebinding would break it?
If I may offer how my LAN is setup ?
-
pfSense router with two interfaces
– 192.168.0.x = main (VLAN 1) subnet
– 192.168.64.x = isolated (VLAN 1003) subnet - (1003 is the Apple guest network tag)
– Connected to core switch which is PVID 1 native, 1003 tagged -
WiFi AP also connected to core switch is PVID 1 native, 1003 tagged
-
Core switch - Netgear XS724EM
-
All other devices are PVID 1 only (all my servers and workstations)
-
pfSense provides DHCP (MAC reservation) for those devices assigned to guest network.
In this configuration, my regular WiFi devices (phone, tablet, TV, etc) are automatically on VLAN 1 (main) and have access to my servers.
By assigning IP address 192.168.64.x to all isolated devices, those devices are forced into VLAN 1003 and automatically isolated at the switching layer by the core switch
I am assuming that the other VLANs on your network that you want to treat as “local” you have their subnets in the settings, right?
It’s in the dashboard, under Settings, Network, LAN Networks and you comma separate the CIDRs. Here is mine as an example:
192.168.250.0/24,192.168.253.0/24,10.97.0.0/28,192.168.254.0/24
192.168.250.0/24 My default VLAN
192.168.253.0/24 My IoT network
10.97.0.0/28 Work from home network
192.168.254.0/24 My Guest Network
That should work just fine.
You have different VLAN IDs for the ports where the devices connect to the switch?
I ‘technically’ have 2 VLANS with 3 subnets
- main - ID 1 - which is the default for all switches (192.168.0.0/24)
- Guest - ID 1003 - Apple/Guest (192.168.64.0/24)
- Work - ID 1 - Plex HQ NAS Lab ( 10.0.0.0/16)
PfSense has the site-site VPN routing 10.0.0.0/24 internally.
Yes, of course. VLAN1 (I Know I should not use that–maybe whenever I change switches) = default. VLAN 2 is work from home. VLAN 3 is IoT. VLAN200 is guest. If I could figure out my remote situation, I would move streaming to VLAN4 and build another subnet and necessary firewall rules. Half tempted to also segregate wireless from wired devices, too.
It you use switched VLANs, you don’t need firewall rules unless you want controlled crossing between them. The VLAN is a hardware firewall because of how the switch operates.
I could have one, completely flat, subet – controlling isolation solely by which switch ports are in use.
Any suggestions on my setup?
Well, both switches are VLAN capable (managed) but in my scenario, it shouldn´t be necessary, as those networks a physically separated. The Plex server has two separate network interfaces to connect to the two networks. The question is now, does every plex client (tv/tablet/smartphone/…) know the right IP of the server, or is it necessary to manually set the IP in the client’s settings?